Critical GitLab vulnerability allows hackers to perform remote code execution

GitLab is requesting users to update branches 15.1, 15.2 and 15.3 of community and enterprise editions to fix a critical flaw that would allow attackers to perform a remote code execution on Github import. GitLab has 30 million registered users and 1 million customers.
What is critical about this GitLab vulnerability?
The flaw is tacked as CVE-2022-2884 and comes with a criticality score of 9.9. It impacts all versions from 11.3.4 to 15.1.4, 15.2 to 15.2.3 and 15.3. Remote command execution is a potent type of flaw allowing hackers to execute malicious code on target machine, deploy malware and take control of the device.
With this flaw, the hackers can take control of the server and extort the source code, execute any malicious intents and more. The flaw is being fixed in 15.3.1, 15.1.5, and 15.2.3, and GitLab is requesting users to upgrade them immediately.
Alternate solution to handle the GitLab vulnerability
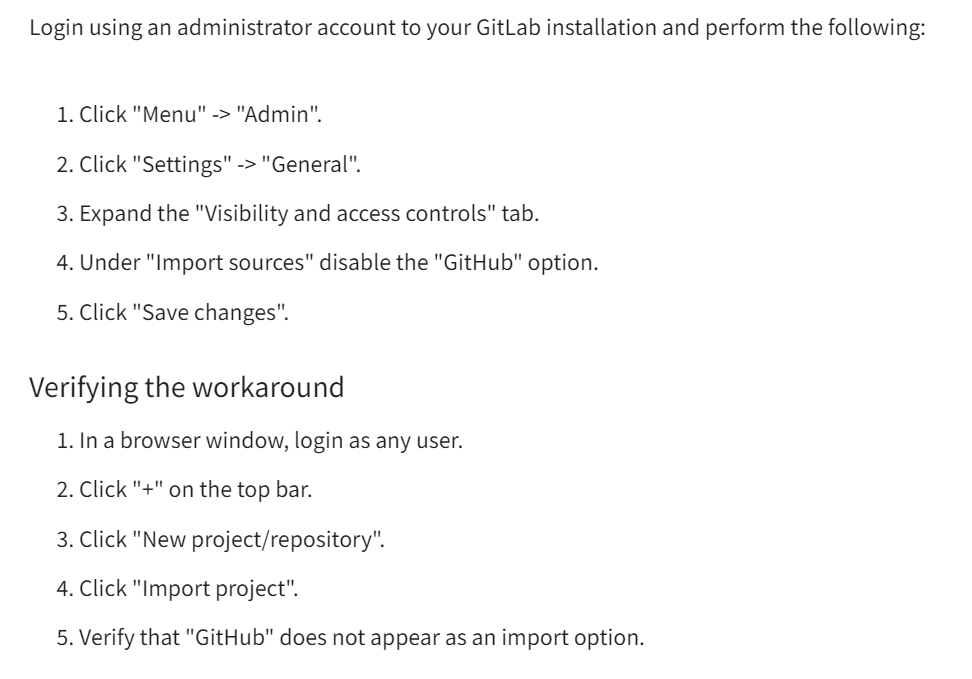
If for some reason it isn’t possible for you to update the versions, GitLab has given an alternate solution which involves the disabling of GitHub import, a tool used for importing projects from GitHub to GitLab.
You can check the workaround below as per GitLab vulnerability announcement,
Though there is an alternate solution for this vulnerability, the best solution is to update the same to latest secured versions for utmost security of your projects and clients. Since this GitLab vulnerability is marked with a severity score of 9.9, it is highly likely to see a exploitation of the same in the wild.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, and Twitter.
You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.








