Ford data breach has exposed sensitive information and databases

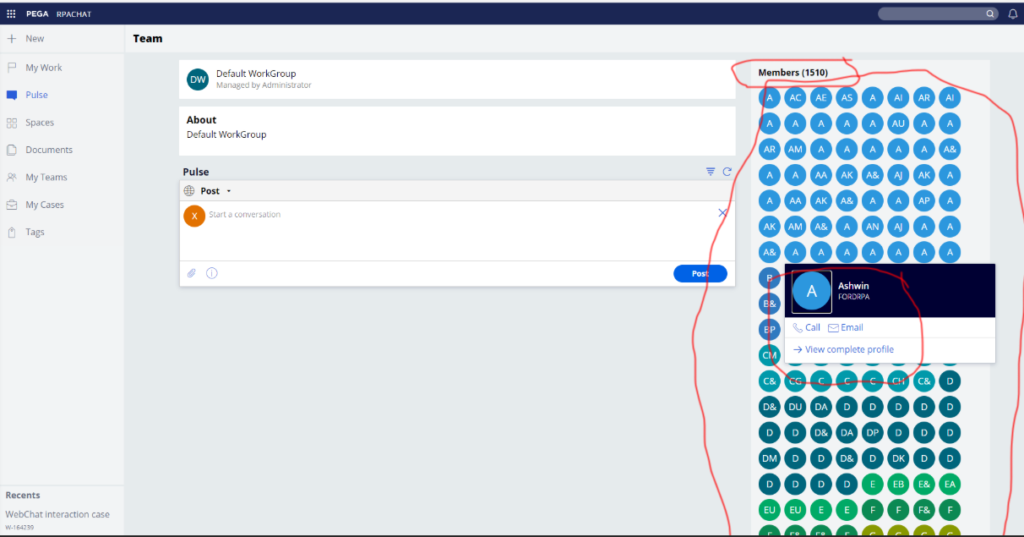
Ford Motor Company has experienced a sensitive data breach via its Pega Infinity customer engagement system which is hosted on Ford’s server. The breach is seen in customer databases, internal tickets and employee records.
Identifying the Ford data breach and vulnerability
Researchers have identified a vulnerability in Ford’s website that has allowed the threat actors to gain access to company records, internal tickets, employee details and proceed with account take overs. The vulnerability was identified by break3r and Robert Willis along with John Jackson, Jackson Henry and Aubrey Cottle, and Sakura Samurai.
The vulnerability is mentioned as CVE-2021-27653 in the Pega Infinity customer management system in Ford network with the information exposure exploit. Here is the security advisory issued by Pega stating ” Misconfiguration of the Pega Chat Access Group portal in Pega platform 7.4.0 – 8.5.x could lead to unintended data exposure.” The Ford data breach and its extent of data access is yet to be revealed in detail, we will know the complete extent of this data breach only when Ford gives its statement on this incident.
Here are some of the many functions that can be performed with the vulnerability:
— John Jackson 桜の侍 (@johnjhacking) March 5, 2021
Anything within the platform. Included but not limited to: viewing all of that data, opening/closing/modifying tickets, looking at internal workflows, viewing sensitive documents, etc.
Breaking down the Ford data breach further
An attacker had accessed the backend web panel of the Pega Chat Access portal. And then the payloads are provided as URL arguments to execute queries and fetch the data table, accessing the OAuth tokens and execute admin actions on the system.
The following data have been exposed: account numbers, employee records, database names, tables, OAuth tokens, support tickets, user profiles, pulse actions, search bar history and more. Attackers can even perform further actions using the obtained data and the vulnerability including account takeovers. The researcher Willis has mentioned in his blog that the impact of the breach could be larger than estimated, with sensitive records and ample amount of data at stake.
As per the researchers claim, Ford didn’t take the report seriously and didn’t respond in time to the security disclosure claim that the reporters submitted via the HackerOne mediation.
Furthermore, since Ford didn’t have a bug bounty program and also HackerOne had a policy to wait for six months until the disclosure of the vulnerability is made public the researcher had to wait this out and report the same for public interest and that only will be there reward for their research. Also, the researchers have claimed that Ford’s endpoints were still accessible even after Ford mentioned they were taken offline. Ford is yet to respond to the data breach news and researchers claim.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.
You can reach out to us via Twitter or Facebook, for any advertising requests.








