

The new year comes with a new ransomware variant called Night Sky, targeting corporate networks and stealing information in double-extortion attacks.
The discovery of Night Sky ransomware was first made by MalwareHunterteam on Dec 27th when two victims were affected by the ransomware variant. The ransom demand was $800,000for the decryptor and not publishing the encrypted data.
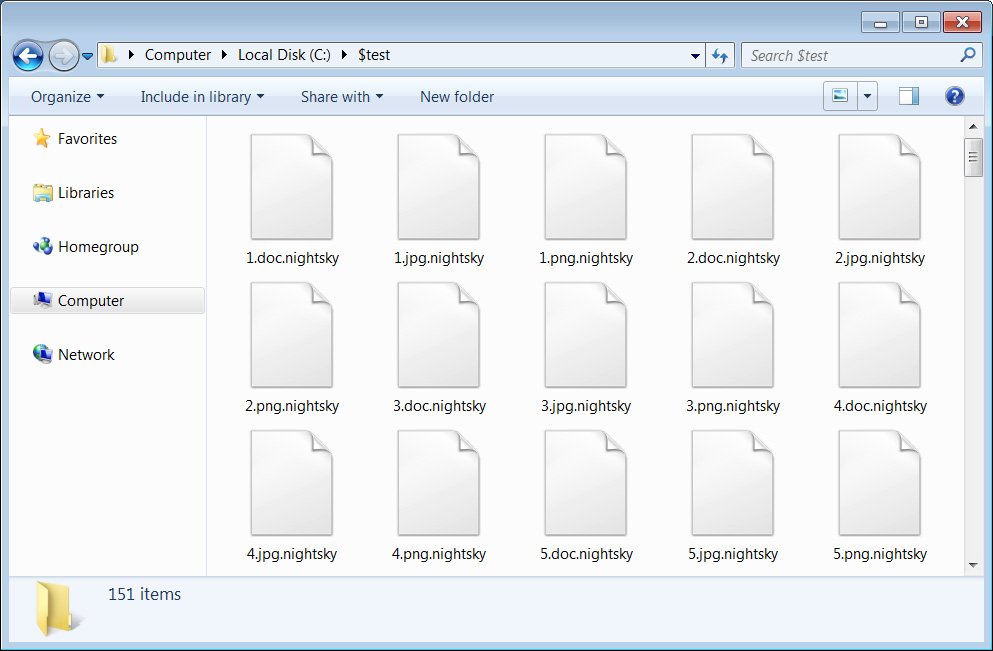
Night Sky ransomware comes with a hardcoded credentials to breach the victim’s negotiation page and deliver a customized ransom note. The ransomware will encrypt your data except the .dll and .exe files. Once the files are encrypted the encrypted files will have a extension .nightsky as the shown in the image.

Within folders a ransom note with file name NightSkyReadme.hta is available, and this file will have the details of the data that is stolen including emails, credentials, etc. The ransomware uses email and web site with Rocket to communicate with the victims.
Also, the ransom note comes with credentials which should be used to login with the Rocket.Chat URL.
Like any other ransomware operations Night Sky ransomware also encrypts as well as steals the victim’s data for further leverage. The double-extortion strategy is used to threaten victims to make ransom payments, as leakage of data could be more devastating than just encryption.
The leakage of data is done via the data like site in Tor which already has the two victims from the December breach. These two victims were from Japan and Bangladesh. The recent ransomware attack was from AvosLocker Ransomware Operators on December 30th attacking the US police department, and Night Sky ransomware is the first ransomware threat of 2022 that security professionals and enterprises need to keep an eye on.
While there has not been a lot of activity with the new Night Sky ransomware operation, it is one that we need to keep an eye on as we head into the new year.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.
You can reach out to us via Twitter or Facebook, for any advertising requests.
Recast Software offers a suite of tools designed to enhance and simplify endpoint management in…
Patch My PC is a widely-used solution that simplifies third-party application management by automating app…
Explore the top 5 best Microsoft Intune alternatives, comparing key features, user reviews, and capabilities…
Discover the top 7 smartphones of 2024 with best security features, offering privacy, performance, and…
Discover the top 11 log management tools for efficient system management and monitoring. Learn about…
Explore the top 5 threat intelligence tools, their features, and how they enhance cybersecurity against…