NSA warns of wildcard certificates and steps for protection

The NSA has issued a warning against the usage of broadly-scoped certificates for multiple server authentication in any organization. A document was released last week with mitigation against the use of wildcard certificates as there is a new technique called ALPACA which could be used for traffic redirection attacks.
ALPACA the silent assassin
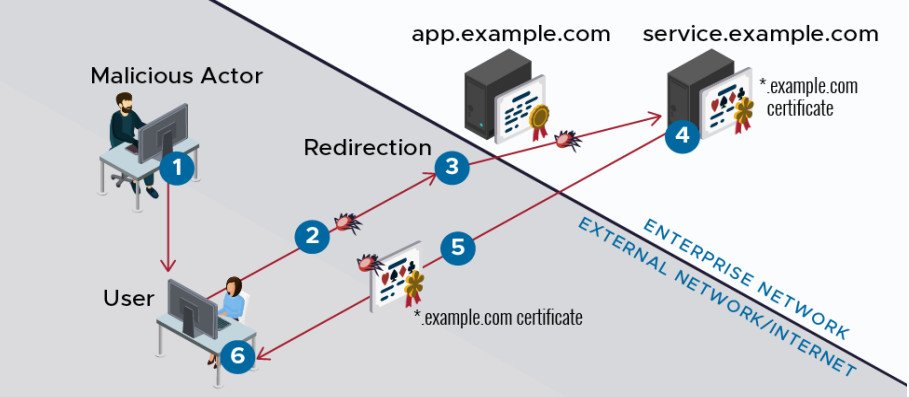
The NSA is warning about the dangers that come with wildcard certificates that validate and allow secure connection to Transport Layer Security Protocol. Researchers have shown that the wildcard certificates can be exploited through an application layer protocol content confusion attack, which was later named as ALPACA – Application Layer Protocols Allowing Cross-Protocol Attack and facilitates cookie hijacking or cross-site scripting attacks.
Wildcard and multi-domain certificates differ from one another, the former is used for sub-domains within a domain, while the latter goes for multiple individual domain under the same IP address. With ALPACA attackers can perform phishing, MITM, watering hole and malvertising attacks on businesses.
To prevent such attacks the private key of the wildcard certificate has to be protected and should be kept in a secured server.
Protecting your wildcard certificates
Organizations should ensure these certificates are used in the appropriate times and their scope should be well studied before using one. The storage location of the private keys has to be periodically tested and ensured of high security. Employing a gateway or firewall is better for enhanced protection and safety.
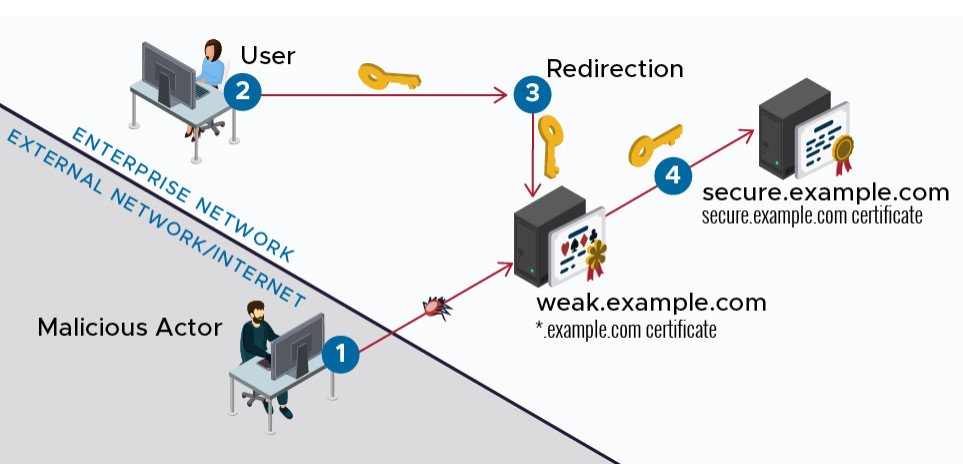
DNS encryption with validation for DNS security extensions can avoid users to land in a different or malicious location. Finally enabling ALPN and keeping your browsers updated can reduce the chances of becoming a victim to ALPACA influenced attacks.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.
You can reach out to us via Twitter or Facebook, for any advertising requests.








