
Purple Fox malware is distributed via malicious Telegram Desktop Installer, this malware installs further payloads on the affected devices.
The file “Telegram Desktop.exe” comes with two files, an original installer file and a malicious downloader.The legitimate installer isn’t executed as the AutoIT program runs the TextInputh.exe file.
This TextInputh.exe when executed will create a new folder called “1640618495” under the C:\Users\Public\Videos\ location and then communicate with C2 to download a RAR and 7z utility. The RAR file contains the configuration and payload file, when the 7z program unzips everything to the ProgramData folder.
As per Minerva Labs, TextInputh.exe does the following actions onto the compromised machine,
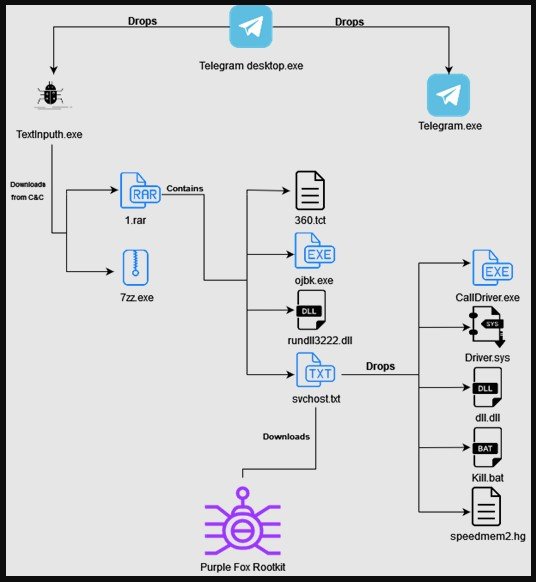
Later, a registry key is created and a DLL disables UAC the payload is executed and the following five additional files are dropped into the infected system,
These extra files is used to block the initiation of 360 AV processes and avoid detection of Purple Fox on the affected device. Moving further the malware gather system details, scans for security tools running in the device and then send the hard coded C2 address.
After this process, Purple Fox is downloaded from the C2 in the form of an .msi file that has encrypted shellcode for both 64- and 32- bit systems. Once the Purple Fox is executed, the compromised devices are restarted for the registry settings to work, especially the disabled User Account Control (UAC).
To achieve this, the dll.dll file sets the following three registry keys to 0:
Disabling bypassing UAC is vital because it deploys viruses and malware with administrator privileges. In general, UAC prevents the installation of unauthorized apps and the change of system settings, to be active on all Windows devices.
When disabled Purple Fox will perform malicious functions like searching of file, exfiltration, deletion of data, process killing, downloading and running code. and even worming to other Windows devices. Malware similar to Purple Fox are actively being distributed via Youtube Videos, malicious websites, and other forum sites.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit. You can reach out to us via Twitter or Facebook, for any advertising requests.
Recast Software offers a suite of tools designed to enhance and simplify endpoint management in…
Patch My PC is a widely-used solution that simplifies third-party application management by automating app…
Explore the top 5 best Microsoft Intune alternatives, comparing key features, user reviews, and capabilities…
Discover the top 7 smartphones of 2024 with best security features, offering privacy, performance, and…
Discover the top 11 log management tools for efficient system management and monitoring. Learn about…
Explore the top 5 threat intelligence tools, their features, and how they enhance cybersecurity against…