ViperSoftX Malware Targets Password Managers and Cryptocurrency Wallets

Trend Micro researchers have reported a new version of the ViperSoftX information-stealing malware that can target more browsers and password managers.
The malware’s latest iteration features stronger code encryption and anti-detection capabilities, making it difficult for security software to detect.
What is ViperSoftX malware?
ViperSoftX is an information-stealing malware that infects computers, stealing various data. The newest version of the malware targets password managers such as 1Password and KeePass 2, as well as cryptocurrency wallets, including Armory, Atomic Wallet, Binance, Bitcoin, Blockstream Green, Coinomi, Delta, Electrum, Exodus, Guarda, Jaxx Liberty, Ledger Live, Trezor Bridge, Coin98, Coinbase, MetaMask, and Enkrypt.
The malware now targets a range of browsers, including Chrome, Brave, Edge, Opera, and Firefox. According to the report, the malware typically arrives as software cracks, activators, or key generators hidden within benign-appearing software.
Global Targets of ViperSoftX Malware
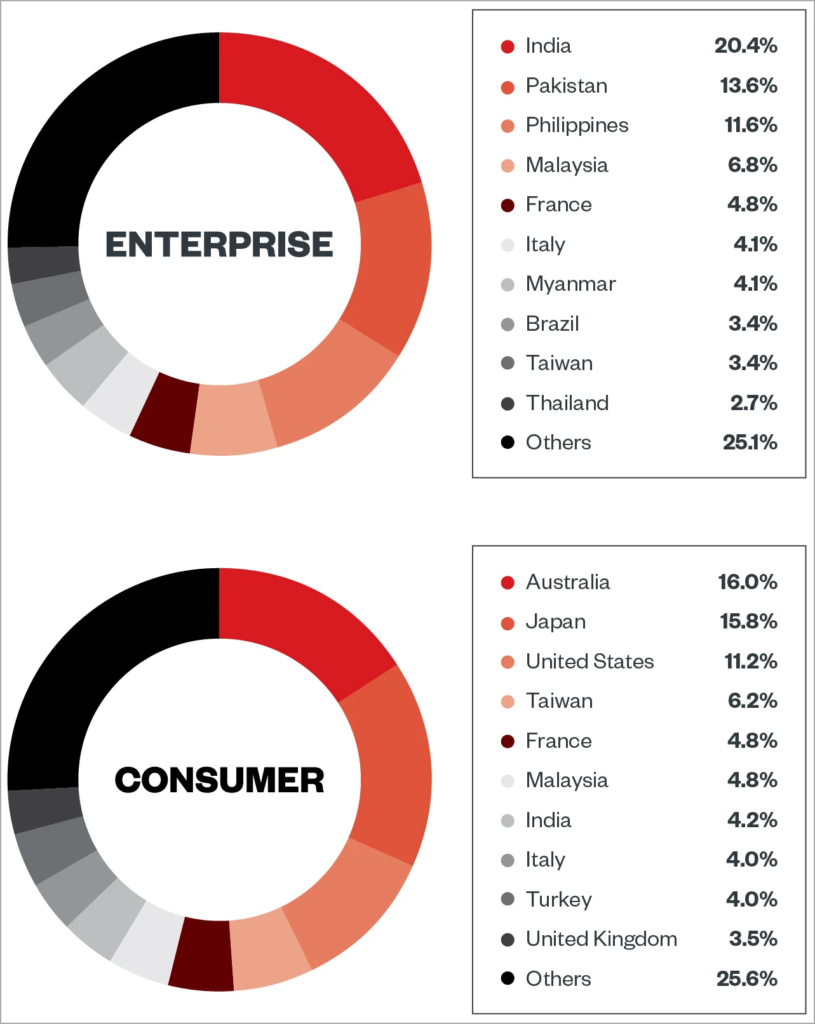
The malware targets both the consumer and enterprise sectors worldwide, with over 50% of the detected activity originating from Australia, Japan, the United States, India, Taiwan, Malaysia, France, and Italy.
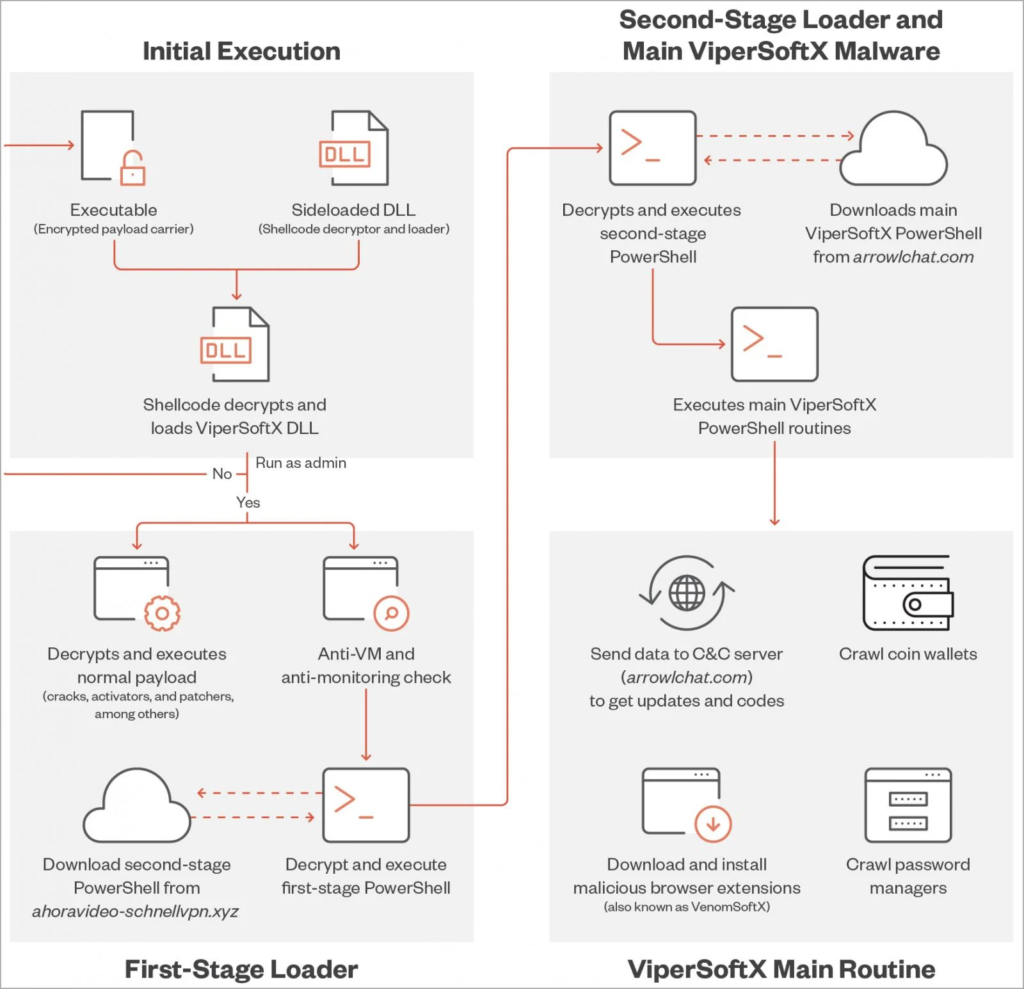
The new version of ViperSoftX employs several anti-detection, anti-analysis, and stealth-boosting features, including DLL sideloading to execute on the target system in the context of a trusted process, byte mapping to encrypt its code, and a communication blocker on web browsers.
The malware’s increased functionality highlights the importance of better security measures and stronger passwords for both consumers and businesses to avoid falling victim to information-stealing malware.
Better Protection Against Detection and Analysis
The new version of ViperSoftX malware has also been designed to evade detection and analysis by security software. It now employs several anti-detection and anti-analysis features, such as the use of DLL sideloading to execute on the target system in the context of a trusted process, avoiding raising any alarms.
Upon arrival, the malware checks for specific virtualization and monitoring tools, such as VMWare or Process Monitor, and antivirus products like Windows Defender and ESET before it proceeds with the infection routine.
The malware also uses “byte mapping” to encrypt its code, remapping the arrangement of shellcode bytes to make decryption and analysis without the correct map much more complicated and time-consuming.
Furthermore, each sideloader DLL has its own pair of executable and byte map. A decryption attempt returns an incorrectly rearranged shellcode if used with another ViperSoftX-related executable, ensuring that the shellcode will not be decrypted without the correct DLL containing the correct byte map.
Communication Blocker
Finally, ViperSoftX features a new communication blocker on web browsers. This feature makes C2 infrastructure analysis and malicious traffic detection harder.
Targeted Sectors and Countries
The report by Trend Micro indicates that ViperSoftX targets both the consumer and enterprise sectors. Furthermore, the countries with the highest number of detected activity include Australia, Japan, the United States, India, Taiwan, Malaysia, France, and Italy, accounting for over 50% of the total detected activity.
ViperSoftX is an information-stealing malware that targets a wide range of browsers, cryptocurrency wallets, and, most recently, password managers. Its new version has stronger encryption, a broader range of targets, and better evasion techniques to avoid detection by security software.
As always, users are advised to exercise caution and take appropriate security measures to protect their devices and sensitive data from malware attacks.








